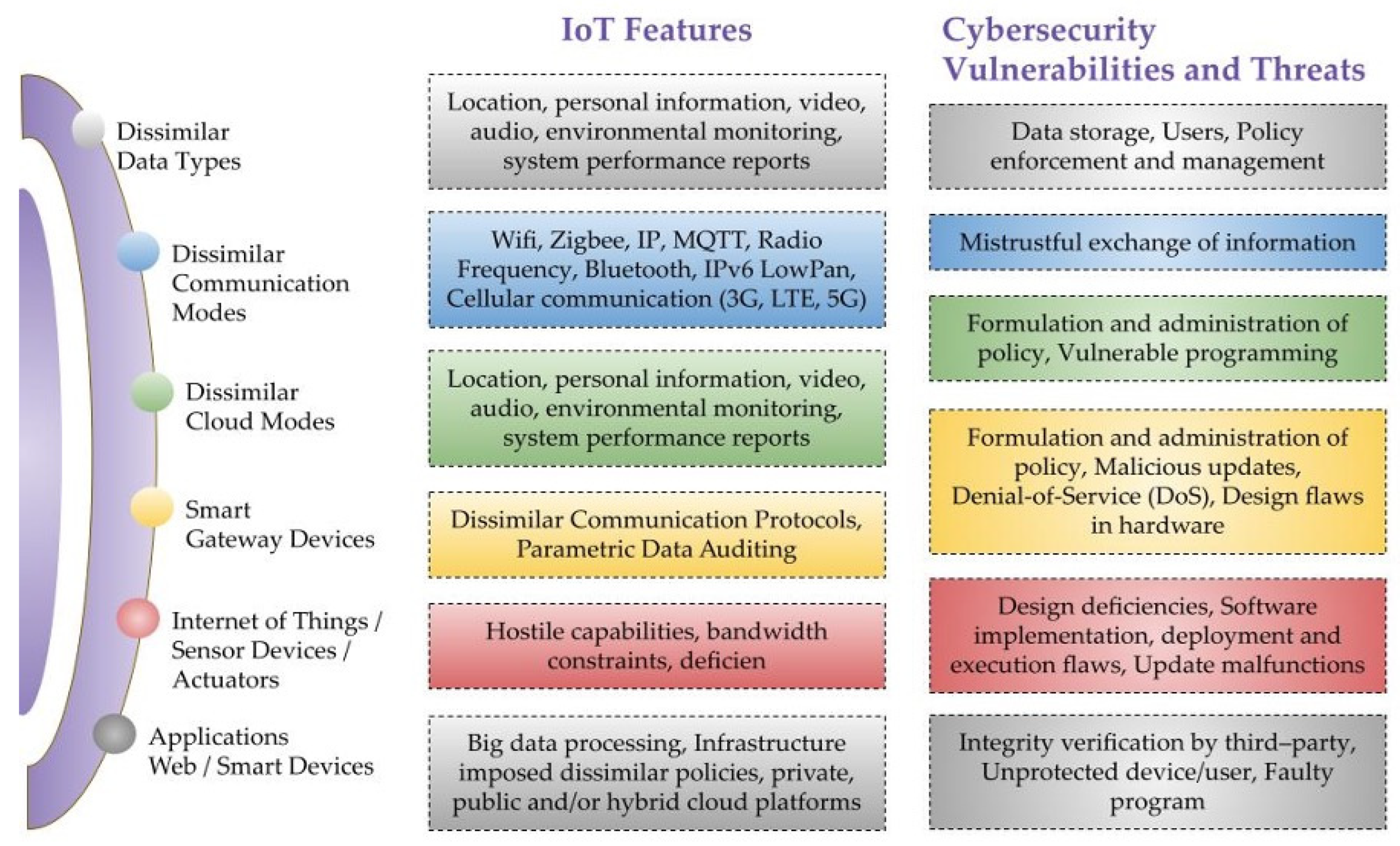
Sensors | Free Full-Text | A Critical Cybersecurity Analysis and Future Research Directions for the Internet of Things: A Comprehensive Review

Hardware Vulnerabilities: How You Can Do Everything Right And Still Be Compromised | by Rohan Kulkarni | PALOIT | Medium
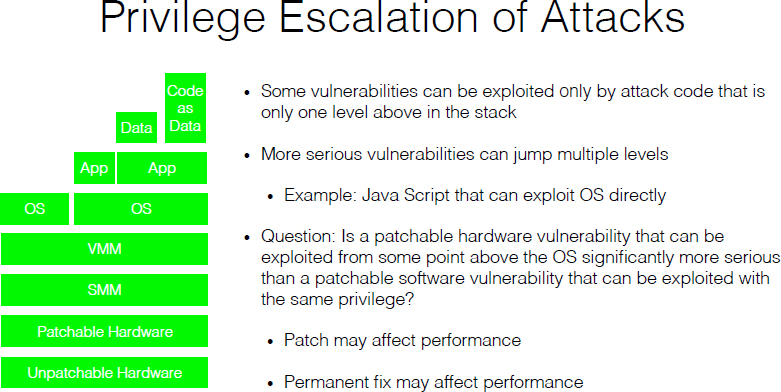
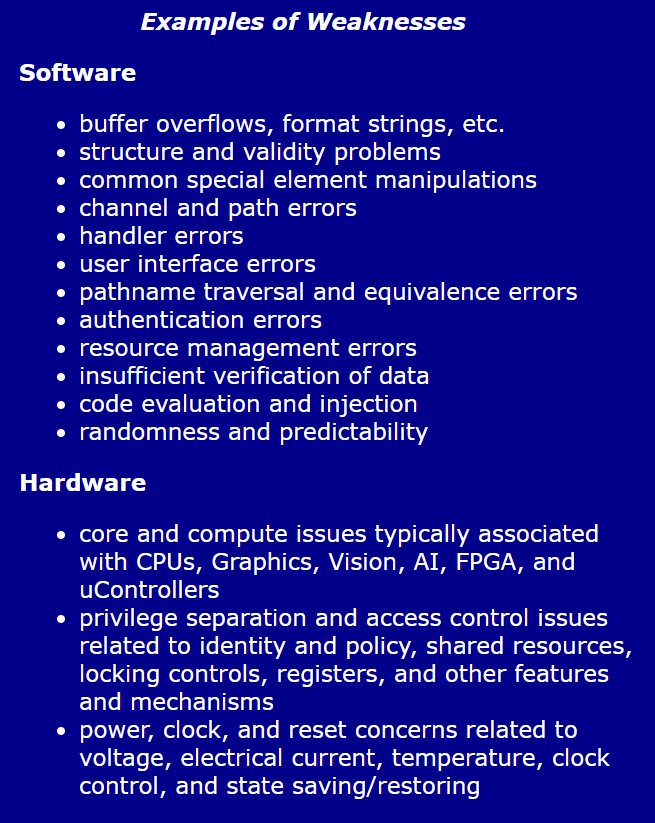
2 Hardware and Software Engineering Assumptions at Risk | Beyond Spectre: Confronting New Technical and Policy Challenges: Proceedings of a Workshop |The National Academies Press