Ccmart Laptop Cable Lock Safety Lock Anti Theft Security Hardware Cable Lock Kit with 2 Sturdy Cable Two Keys 3 m Adhesive Disk for Laptop, PC, Laptops, Mobile Phones and Projectors: Amazon.de:
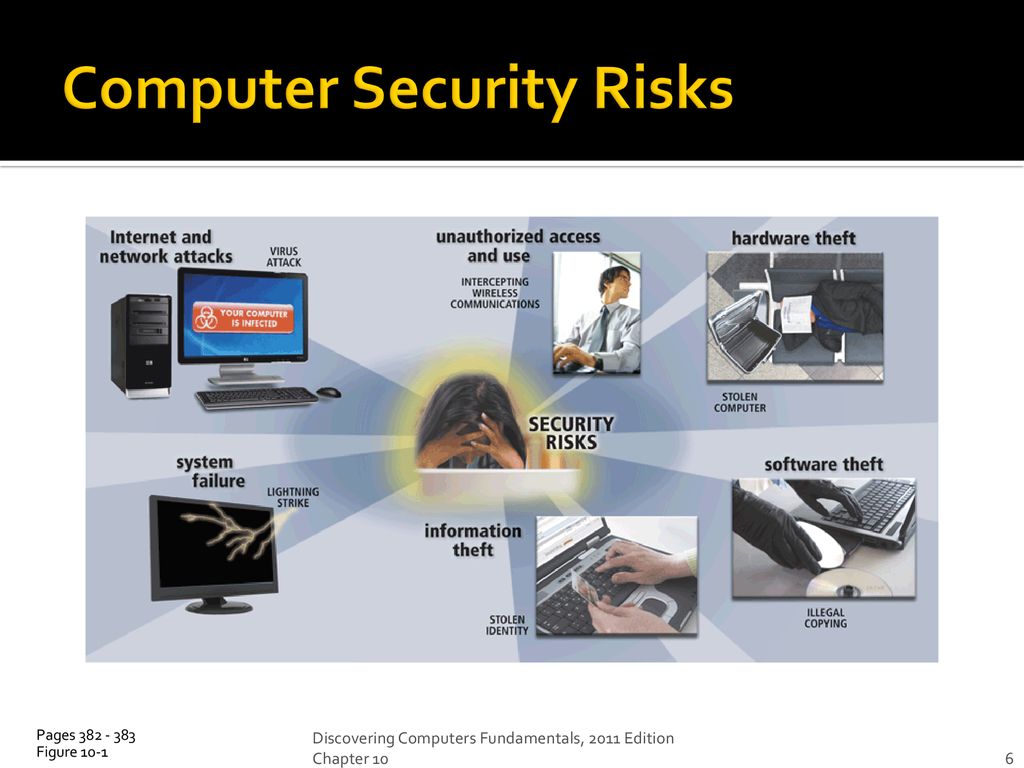
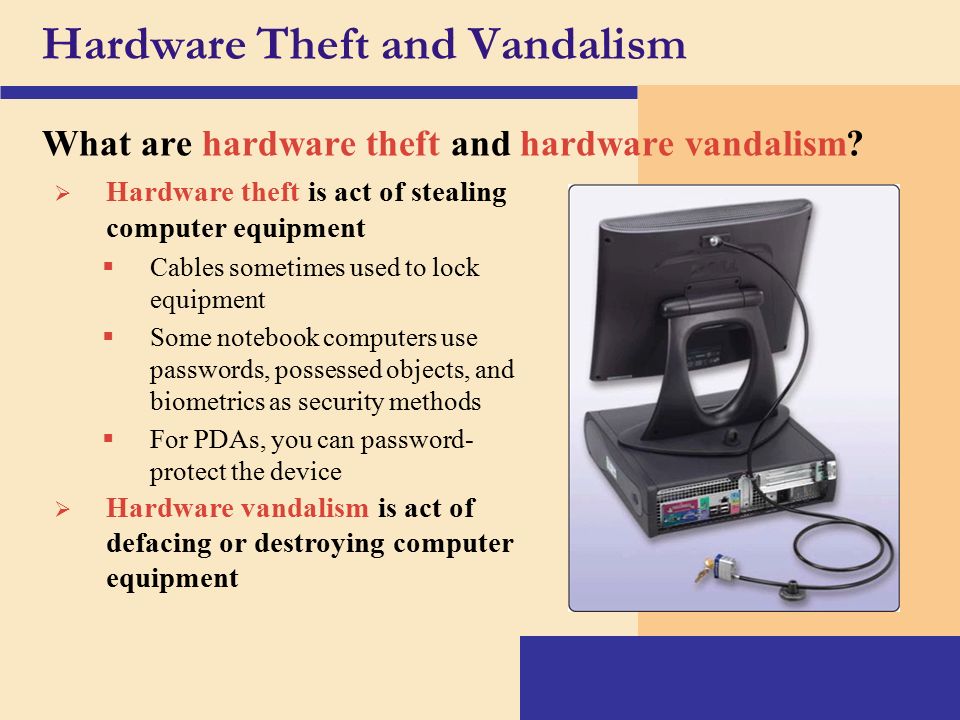
Computer viruses Hardware theft Software Theft Unauthorized access by hackers Information Theft Computer Crimes. - ppt download
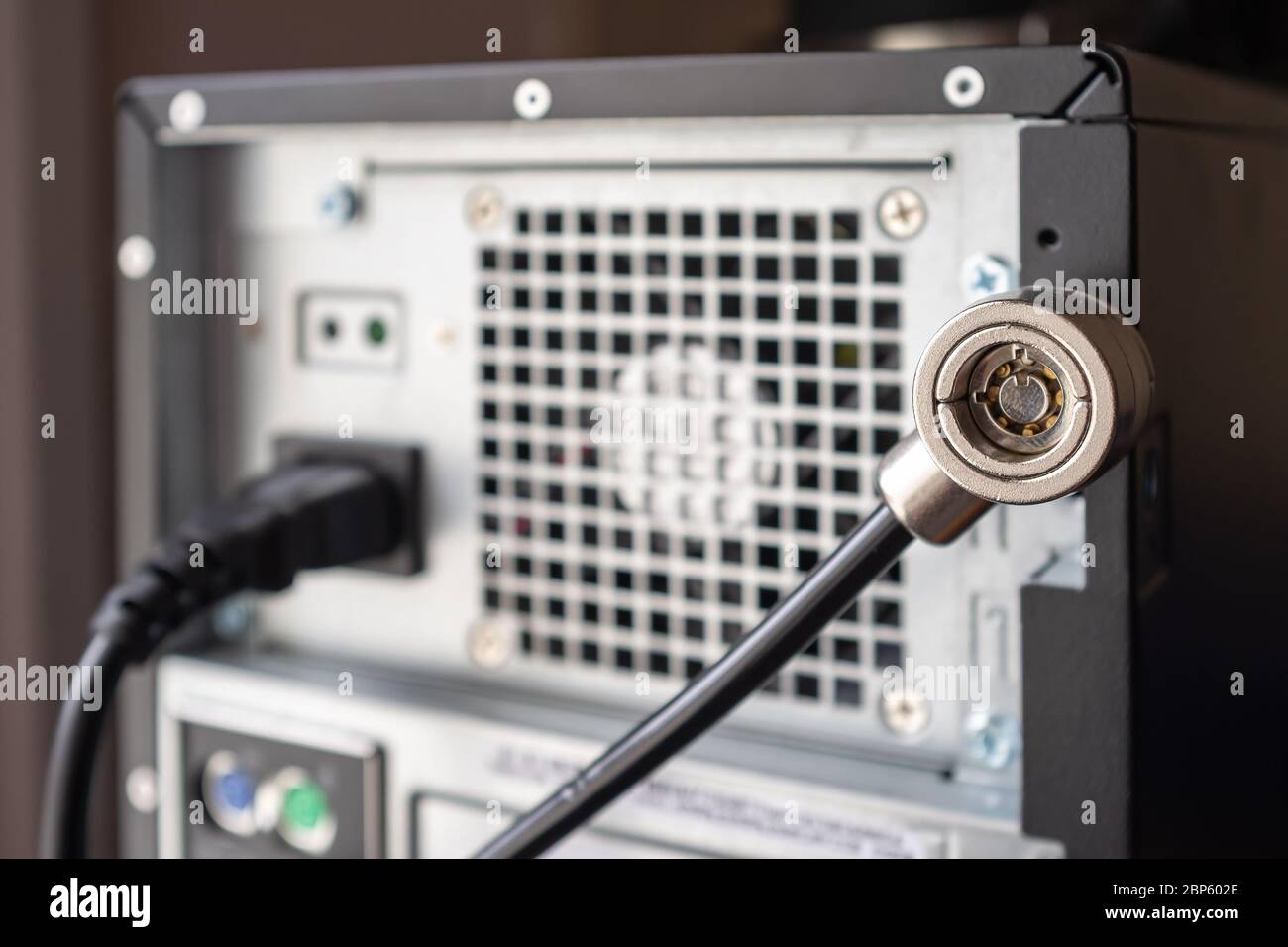
Security lock is installed on the computer to prevent theft and ensure the safety of hardware Stock Photo - Alamy
Computer viruses Hardware theft Software Theft Unauthorized access by hackers Information Theft Computer Crimes. - ppt download